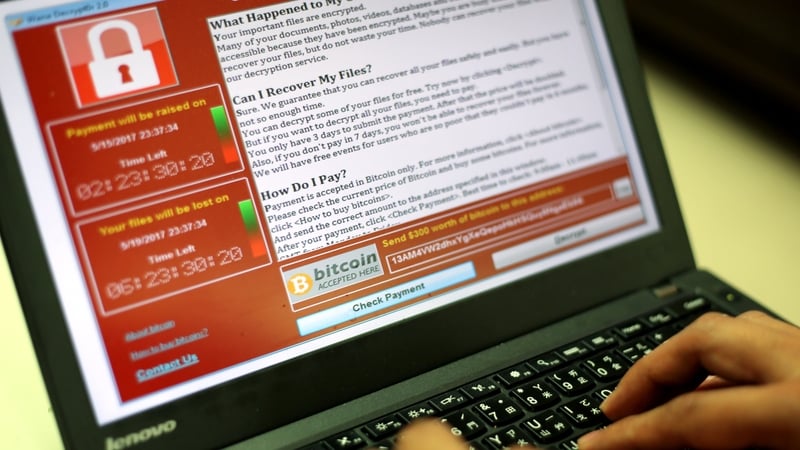
Last year was a bad one for cyber security - with large data breaches at the likes of Equifax, Ransomware like WannaCry affecting hundreds of thousands of users, and historic hacks at companies like Yahoo and Uber coming to light.
That is before allegations of digital interference in international elections is added into the mix.
However, Ward Solutions CEO Pat Larkin is warning that things are only going to get worse in 2018 - and he is predicting the outbreak of a full-scale cyber war this year.
"In some respects I suppose it's been happening for the last ten years, it's just been happening very much under the covers," he said.
"There's been major instances happen in Iran, in Ukraine, in Estonia over the last ten years but it's been happening without attributions."
"What's happening now is that international bodies like the NATO are beginning to put a structure in place around such activity - while many countries are beefing up their systems so that they can respond in kind to attacks from 'rogue' nations.
"It's at a level [now] that effectively ground rules and protocols need to be established and that's what's happening at EU, at NATO and at US level," he said.
"They're starting to lay down ground rules for offensive cyber war, they're laying down red lines in terms of what is unacceptable, whether it's interference in elections, attacking critical national infrastructure or businesses.
"That if, I guess, some of those actions happen that potentially then that may lead to a declaration of war in its own right."
This increased weaponisation of cyber attacks means that the nature of cyber security is now changing for individuals and businesses.
While in the past the focus may have been on hackers trying to steal data - either for direct financial gain or to ransom - now attacks may be designed to have a broader economic impact on a country.
Mr Larkin said that there are already examples of cyber attacks being used to damage infrastructure - for example the StuxNet virus was designed specifically to damage Iran's nuclear centrifuges.
Meanwhile the WannaCry ransomware was perhaps an example of a hybrid attack, with financial gain being part of the equation alongside publicity and a statement of intent by the North Korean regime.
"So you see quite insidious, low-grade stuff that happens to a lot of organisations," he said.
"Similarly you see concerted attempts to attack critical national infrastructure - turning on and off the power grid at will, attacking transport infrastructure, financial infrastructure as an instrument of foreign policy."
Ireland and Irish companies may not seem like the obvious target for this type of cyber battle, but attacks often deploy a scatter-gun approach that sees many devices compromised in the process of a target being hit.
Meanwhile Ireland's reputation as a location many multinationals, along with its membership of the European Union, makes it an equally viable target for attackers.
But should an Irish firm or consumer find themselves on the wrong end of a sophisticated cyber attack - one that has the backing of a country's security apparatus - is there much that they can do?
According to Mr Larkin there is a lot that can be done - but it revolves around the tried and tested techniques of improving standards and ensuring individuals do the right thing.
"The collective message is that cyber security is a business risk - it's not an IT risk any more," he said.
"Businesses need to up their game, whether it's to be compliant, to protect their business or reassure their clients and consumers.
"Information security controls are applied to people, process and technology - a lot of people focus inadvertently on technology only but people need to bring the cyber security IQ of their businesses up to par and that's education and cultural awareness.
"Perhaps their strongest control is the human firewall; the person in the business."