A new report reveals a rise in the number of cyber security risks that are originating from within an organisation, known as insider threats.
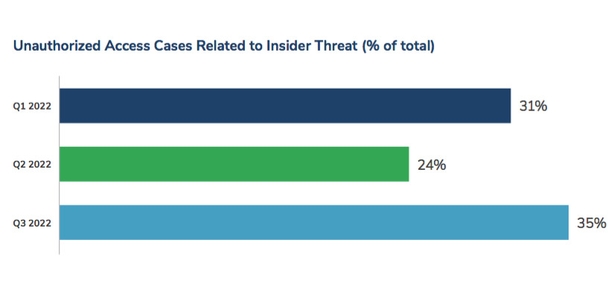
The report by Kroll reveals that insider threats peaked in the third quarter of this year.
Between July and September, such threats accounted for nearly 35% of all unauthorised access threat incidents.
"Insider threat is a unique problem in cyber security," said Jaycee Roth, Associate Managing Director of Cyber Risk at Kroll.
"Unlike the usual circumstances in cyber security, where you are defending the network from external attackers, in an insider threat situation, you are defending the business from someone on the inside.
"This can be particularly difficult, as the user often won't raise any red flags and could have a high level of permissions and access rights," she said.
The report states that companies are at increased risk at the moment, as more people move jobs.
According to the research, exiting employees may seek to steal data or company secrets to publicly undermine an organisation.
Other employees may try to move over data - such as contacts lists and other documents that they can leverage at their new organisations, the report found.
"This becomes ripe ground for possible insider threat, as employees try to retain information on the projects they’ve worked on outside of corporate devices or, in other cases, they retain access rights and permissions for tools and applications they previously used as HR and IT teams struggle to keep up with the amount of staff turnover," said Laurie Iacono, Associate Managing Director for Cyber Risk at Kroll.
Many of the cases Kroll observed in the third quarter of this year coincided with the employee termination process.
To reduce the risk of insider threat, Ms Iacono said companies should pay close attention to the access rights they give staff.
"Monitoring for suspicious activity – such as a particularly large data download or unknown USB device – is another way to spot potential compromises of security," she said.
"Above all, clear instructions to employees on what is and isn’t allowed, combined with fast and efficient IT and HR processes that work together in harmony, will prove the best defense against insider threat becoming a trojan horse," she added.
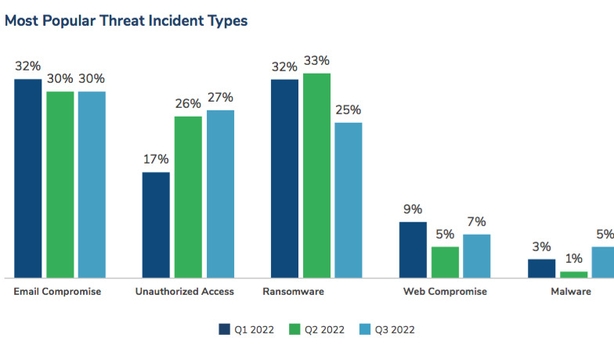
With email compromise plateauing at 30% and the ratio of overall ransomware attacks declining in the third quarter, Kroll observed modest increases in other threat incident types, such as unauthorised access, web compromise and malware.
In recent months, Kroll also observed an increase in USB-based malware cases targeting clients – in part due to the rise in hybrid working.
The report states that many employees now work between multiple devices while working in a number of locations, and use USBs to transfer data.
"In the third quarter of 2022, threat actors and cybercriminal groups were observed sending and dropping USB drives to victims' offices with the intention of operators gaining access to their devices after the USB drives were plugged in," the report states.
In one case, the report reveals that an infected USB device contained multiple malware strains which ultimately attempted to install a cryptominer on the user’s system.
The report states that the positive trends recorded in the third quarter of this year, such as a plateau in email compromise and a decline in ransomware attacks, have been overshadowed by the significant rise in insider threats.
"Organisations are under greater pressure than ever to assess their potential security threats from multiple perspectives, including both external threats and those hidden within the organisation," the report states.







